目录导航
jjjjjjjjjjjjjs简介
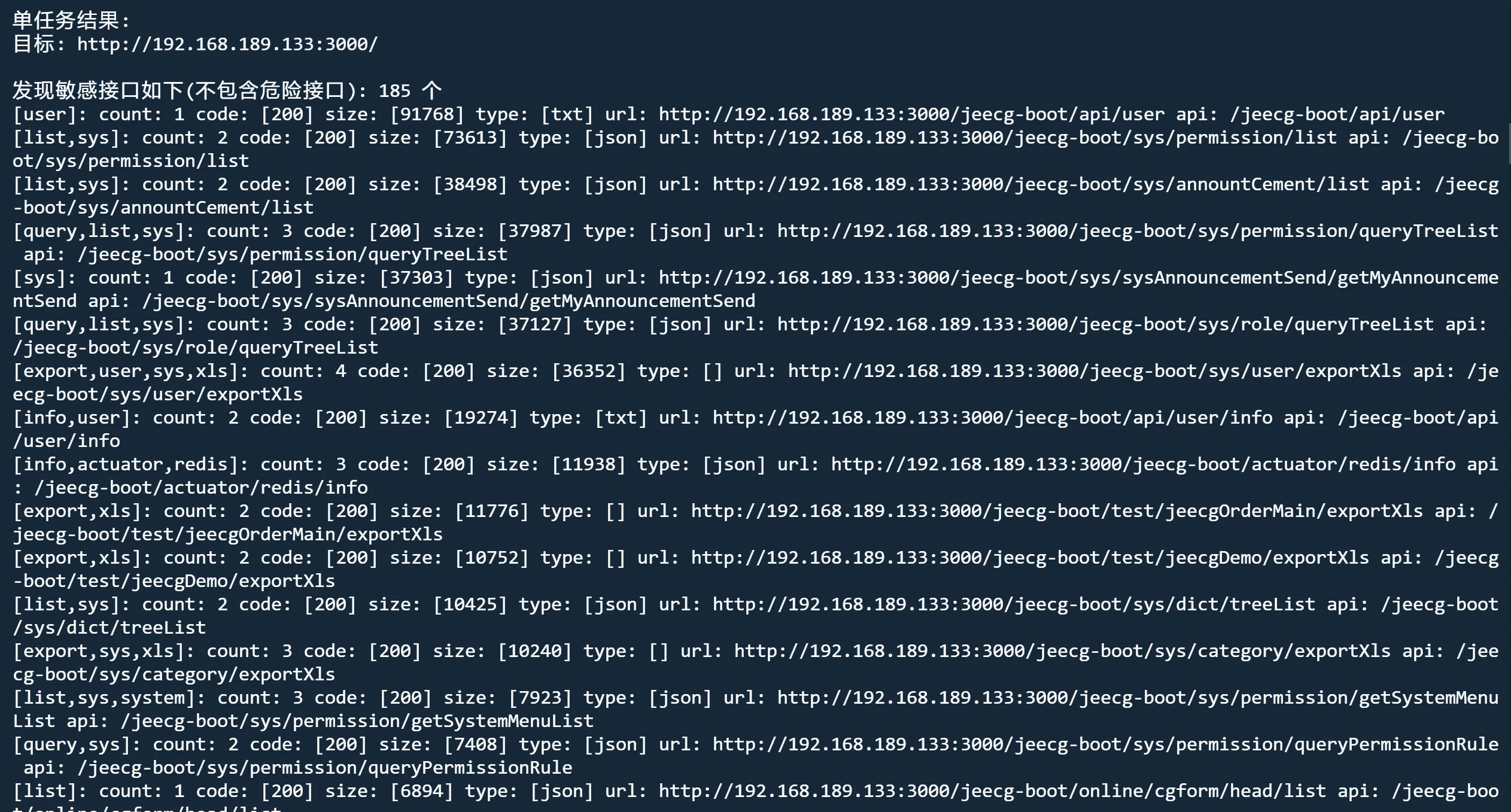
针对webpack站点,爬取网站JS文件,分析获取接口列表,自动结合指纹识别和fuzz获取正确api根,可指定api根地址(针对前后端分离项目,可指定后端接口地址),根据有效api根组合爬取到的接口进行自动化请求,发现未授权/敏感信息泄露,回显api响应,定位敏感信息、敏感文件、敏感接口。支持批量模式。支持需认证接口自动尝试bypass。
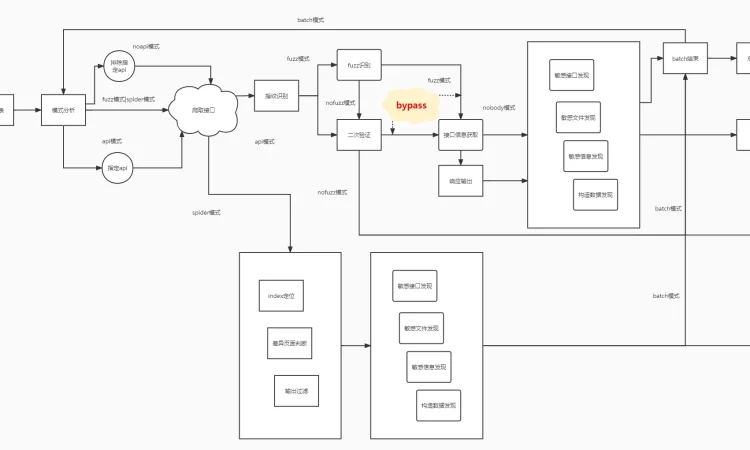
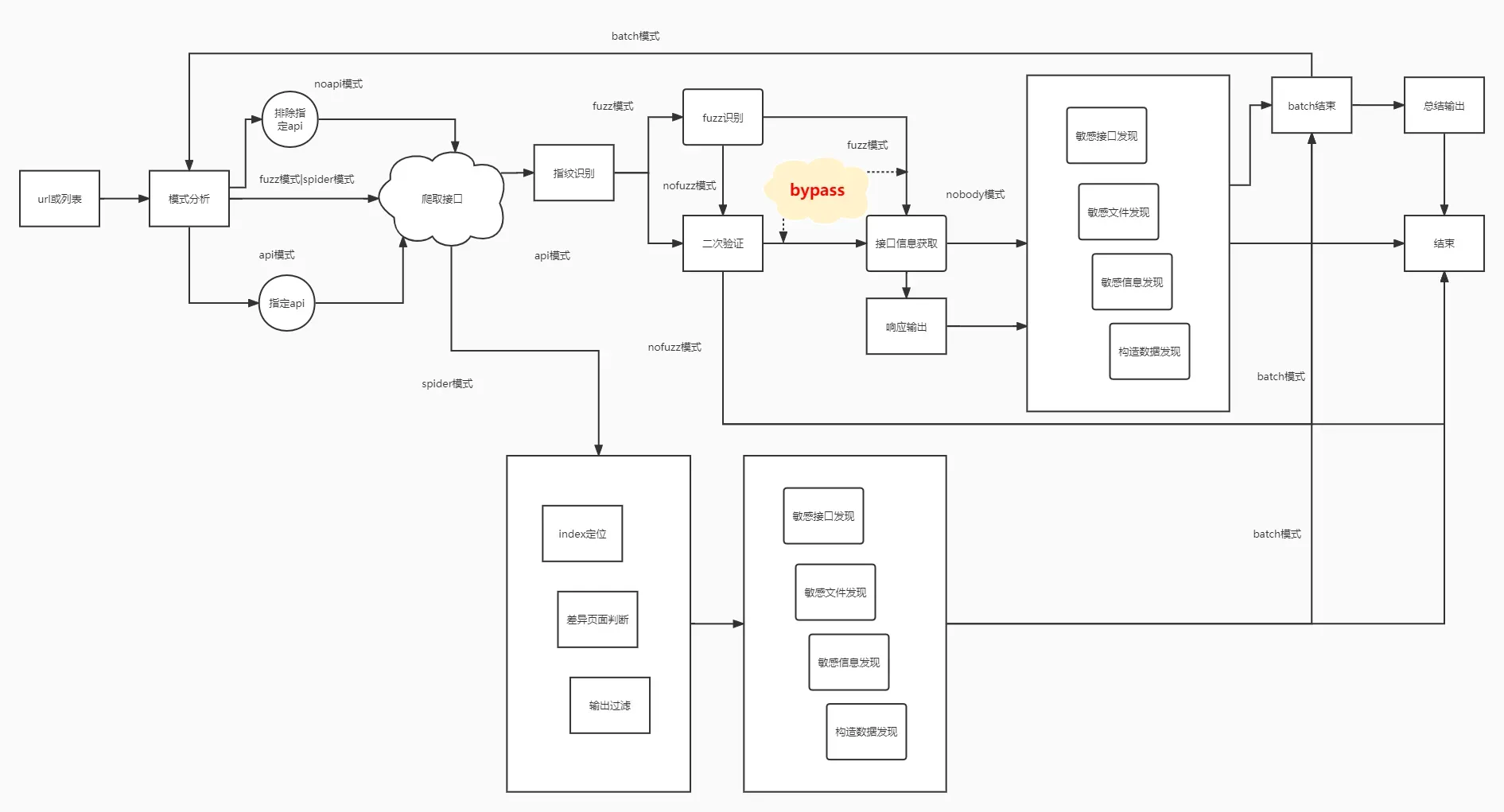
原理流程图
使用
环境:
python3.8
安装依赖:
pip3 install -r requirements.txt使用方式
使用方式:python3 jjjjjjjs.py url|urlfile [fuzz|api] [noapi] [nobody|nofuzz] [cookie] [header] [danger] [bypass] [output] [thread] [proxy] [flush] [deep]
url|file: 目标url
fuzz: 自动fuzz接口
api: 用户指定api根路径 fuzz|api e.g. api=/jeecg-boot 或 api=http://api.test.com/root
noapi: 排除输入的指定api e.g. noapi=/system,/worker,/api
nobody: 禁用输出响应body nobody|nofuzz
nofuzz: 仅获取有效api,无后续响应获取
cookie: 设置cookie e.g. cookie='username=admin'
header: 设置header e.g. header='X-Forwarded-For: localhost\nX-Access-Token: eyJxxxxx'
danger: 解除危险接口限制
bypass: 对500 401 403 进行bypass测试
output: 输出到文件 (txt) e.g. output='dest.txt'
thread: 线程数 e.g. thread=200
proxy: 设置代理 (仅指定proxy时, 自动设置代理到http://127.0.0.1:8080) e.g. proxy='http://127.0.0.1:8080'
flush: 清除项目历史记录, 重新爬取
deep: 深度模式(一般不需要开启), 开启后爬取深度上限:URL 2层 JS 3层,同源URL 3层, 同源JS 5层
debug: 展示更多信息
目标参数的位置固定在参数第一位,其他参数不限制出现位置
注意: 目标参数的位置固定在参数第一位,其他参数不限制出现位置
示例
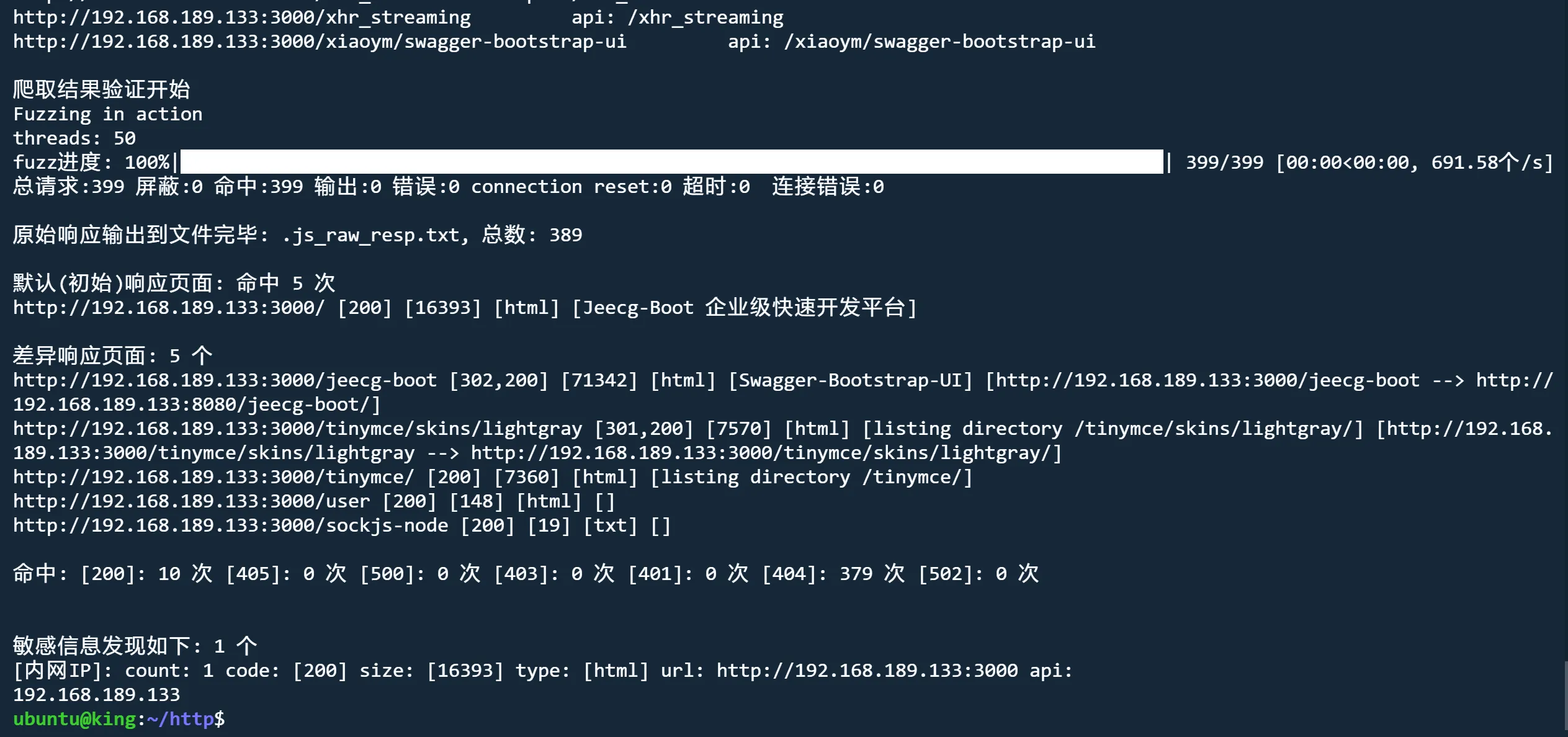
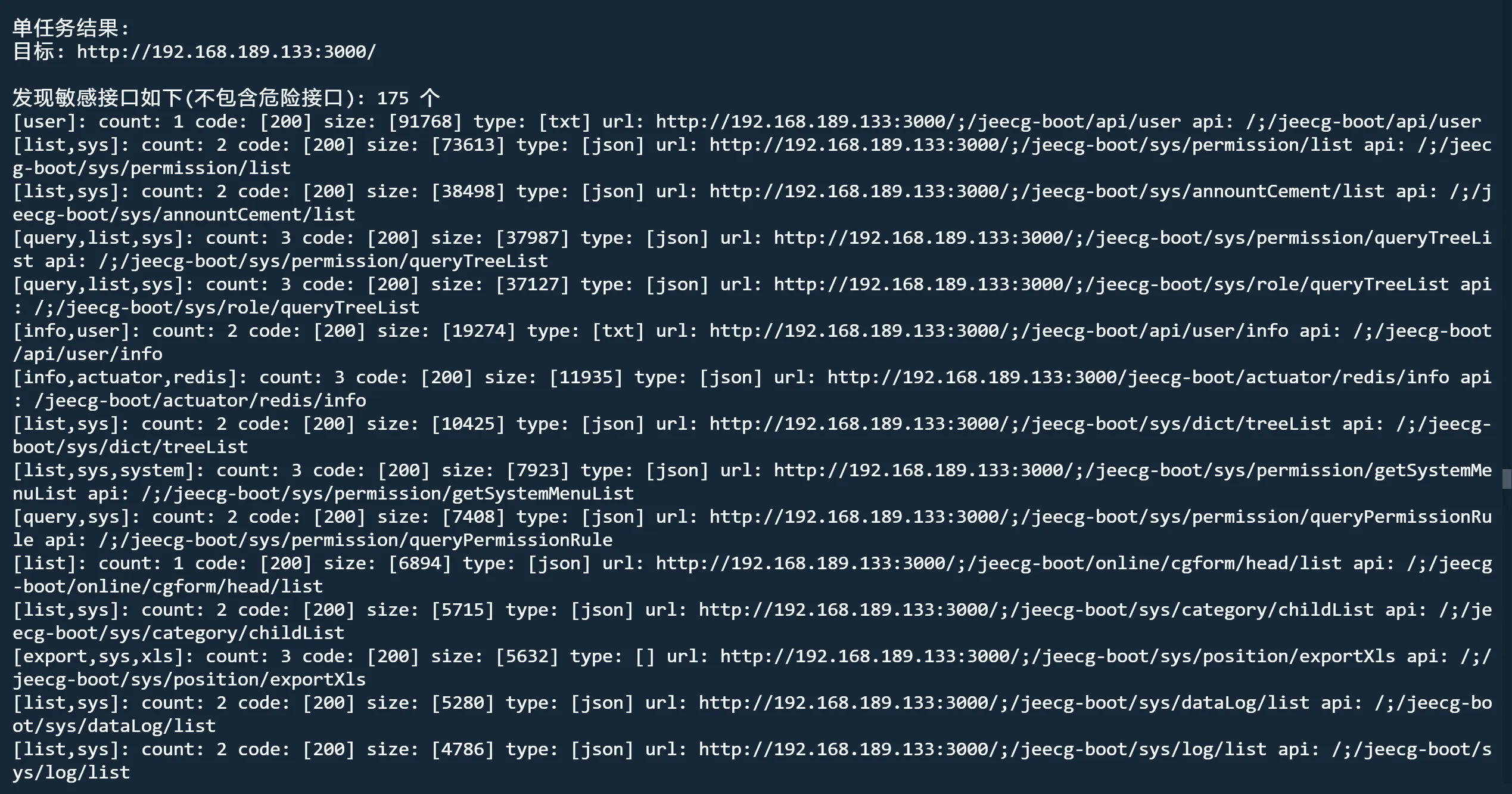
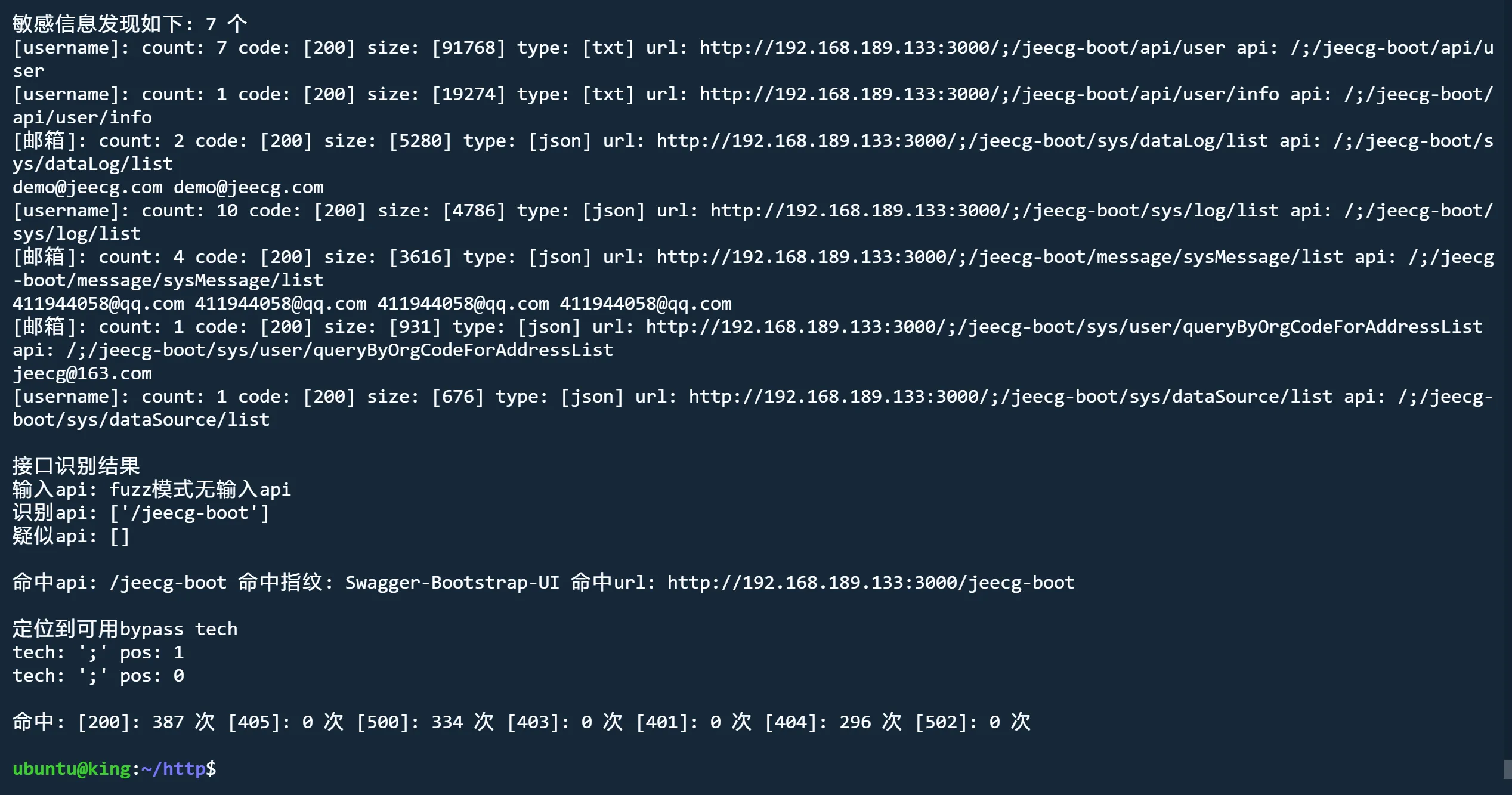
爬取模式
python3 jjjjjjjjjjjjjs.py http://192.168.189.133:3000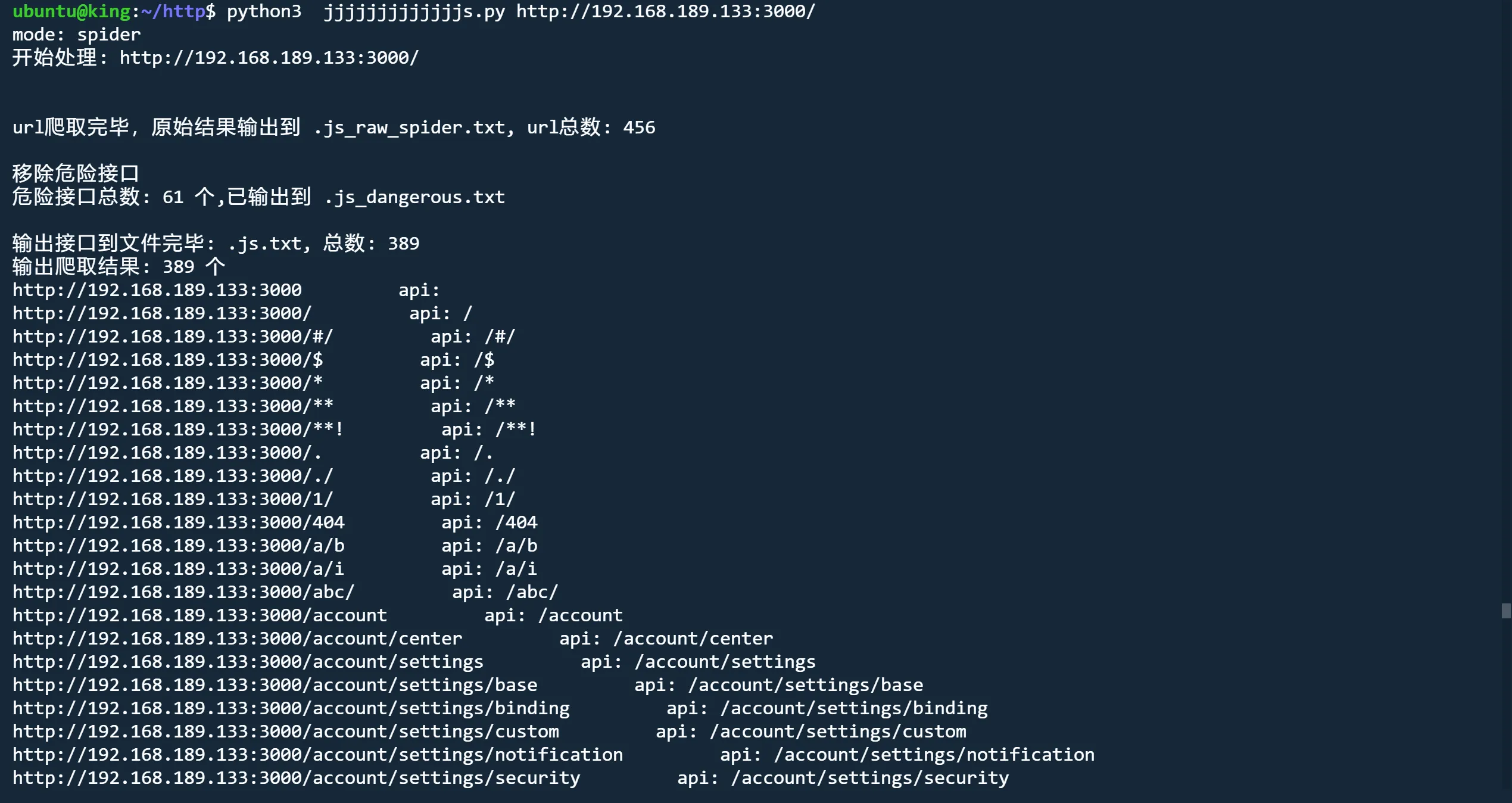
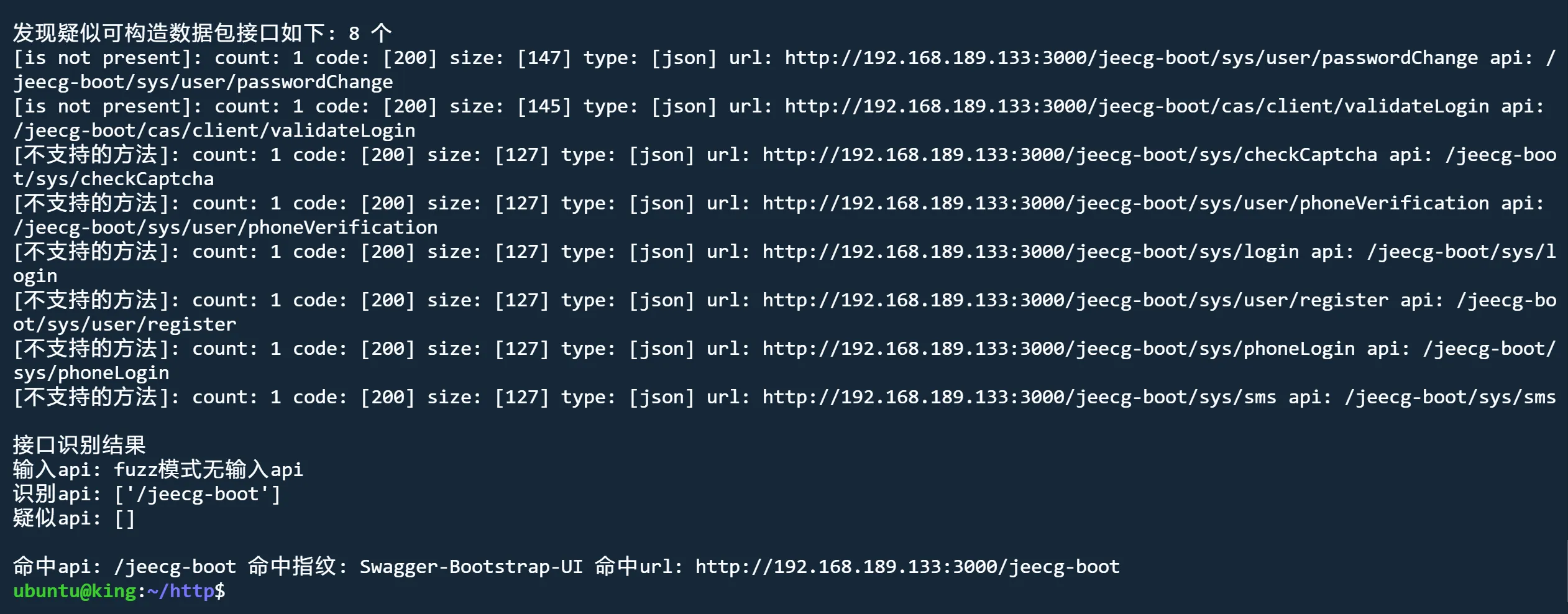
fuzz模式 nobody
python3 jjjjjjjjjjjjjs.py http://192.168.189.133:3000 fuzz nobody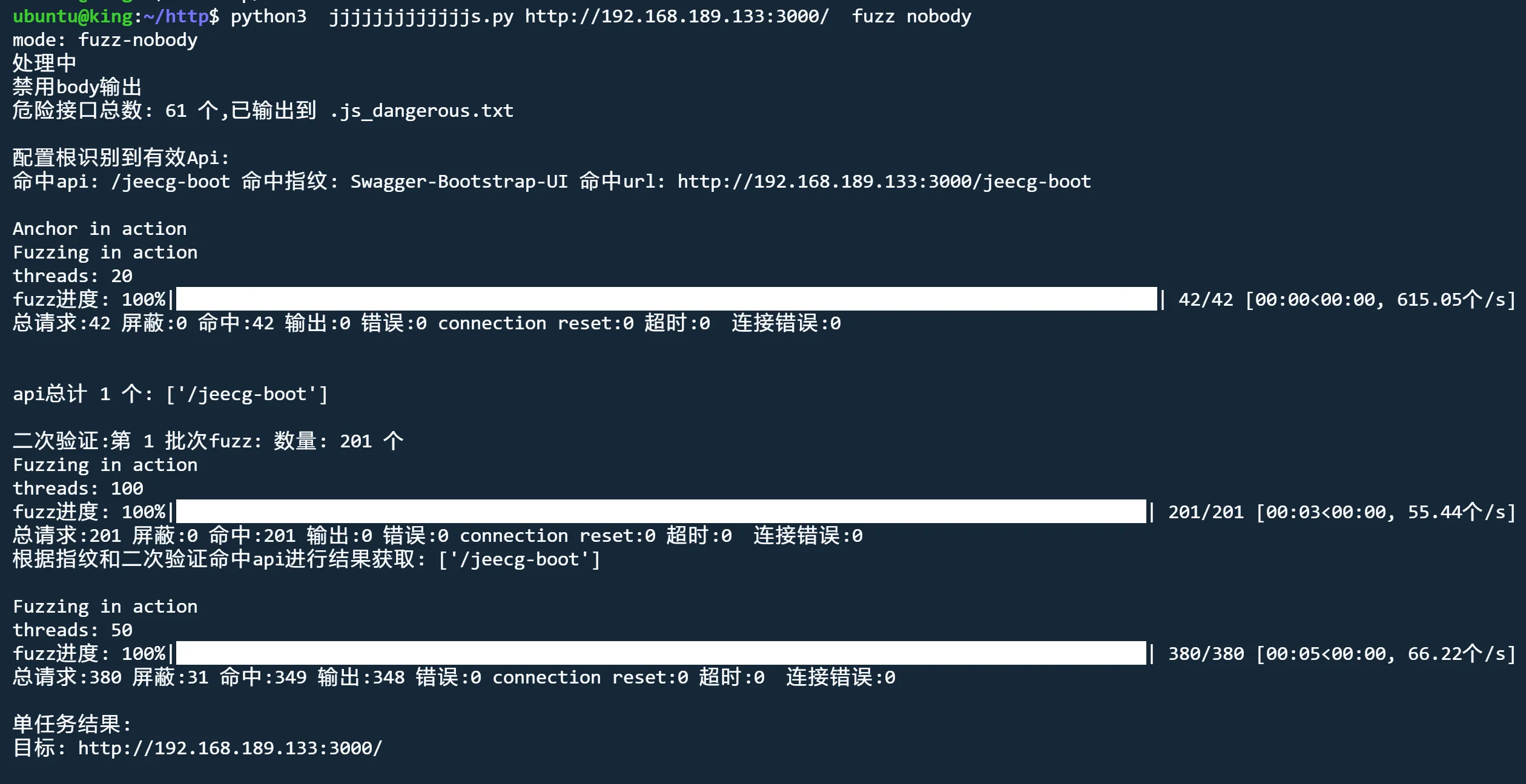
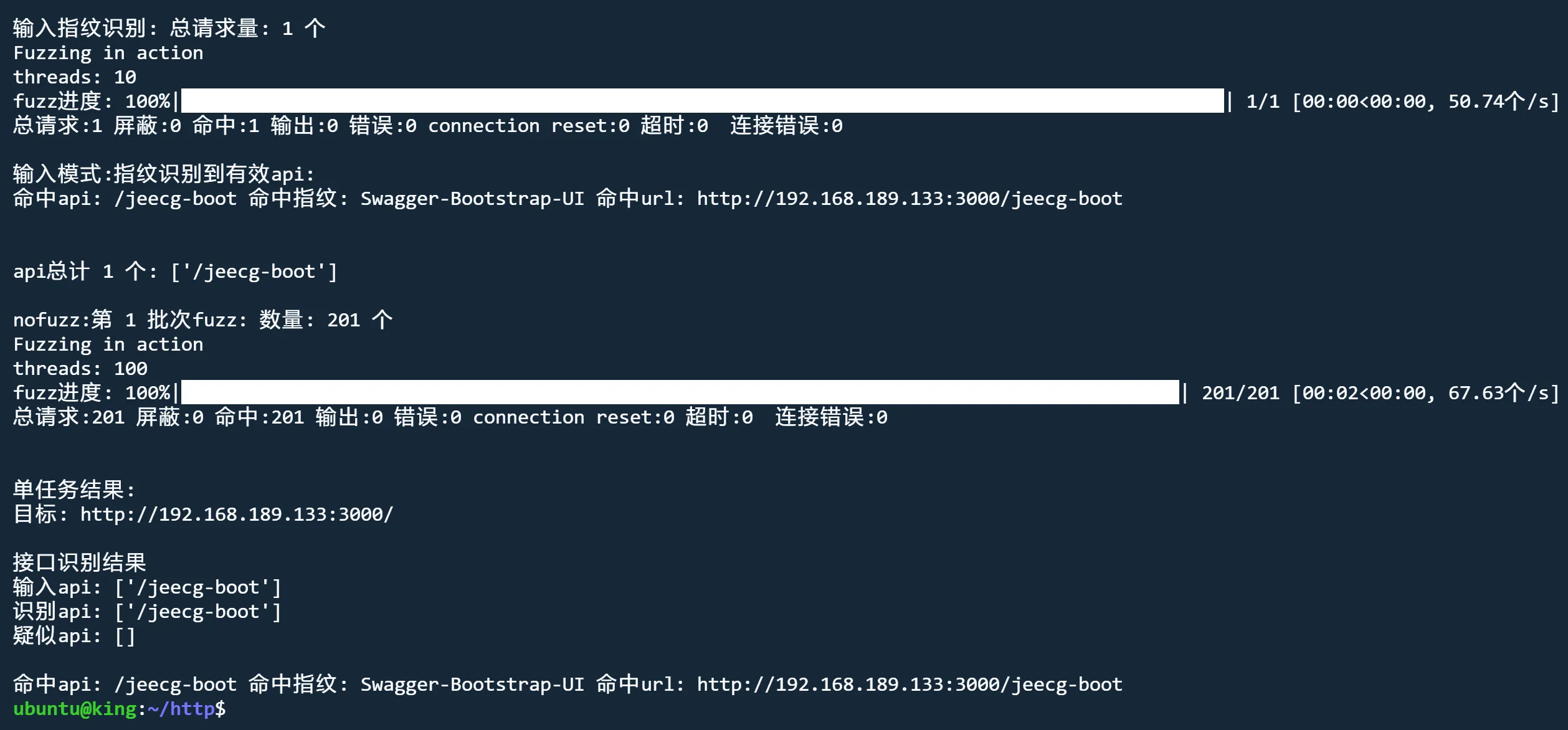
api模式 nofuzz
python3 jjjjjjjjjjjjjs.py http://192.168.189.133:3000 api nofuzz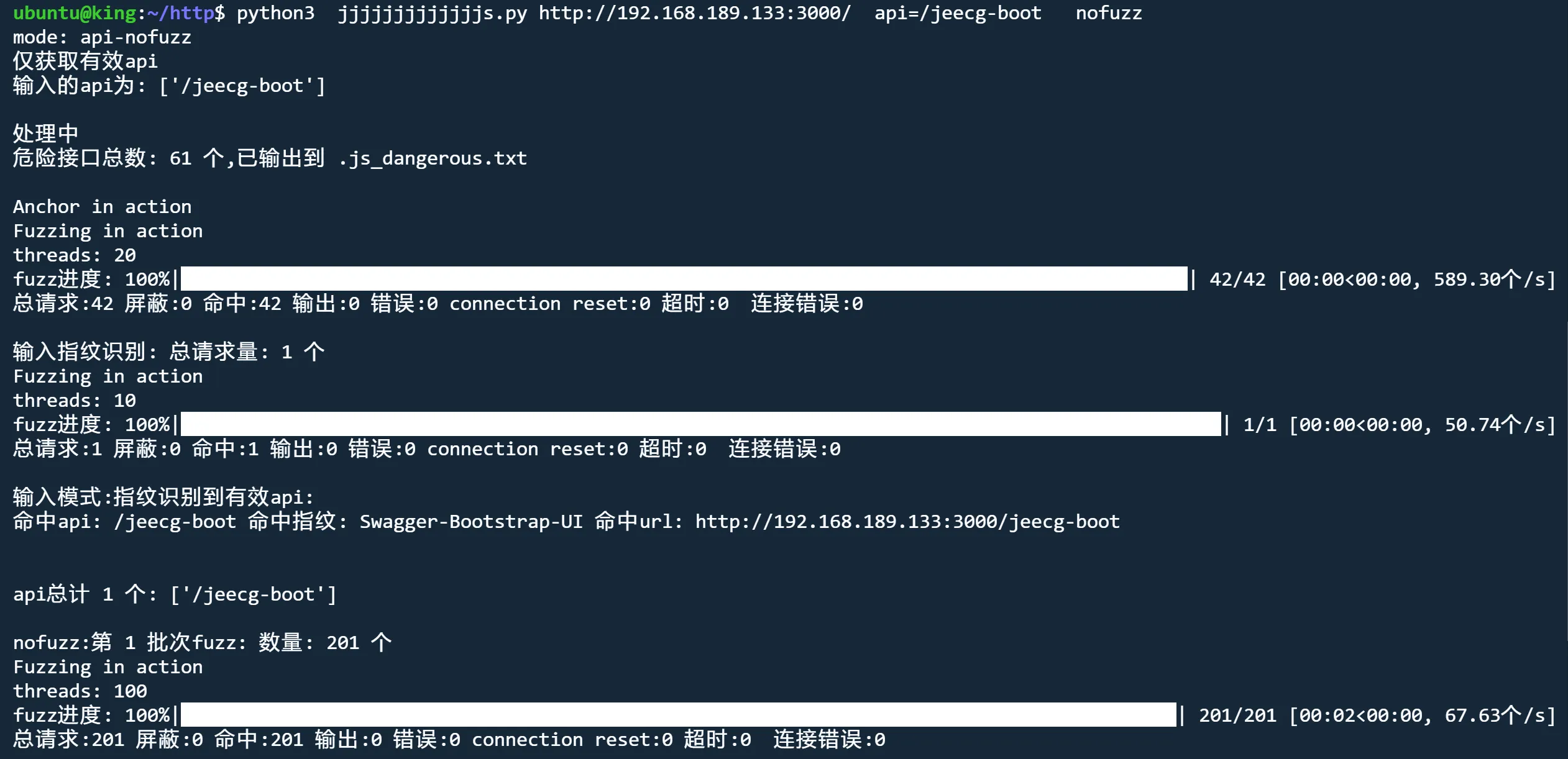
api模式 nobody header
python3 jjjjjjjjjjjjjs.py http://192.168.189.133:3000/ api nobody header='X-Access-Token:eyJxxx'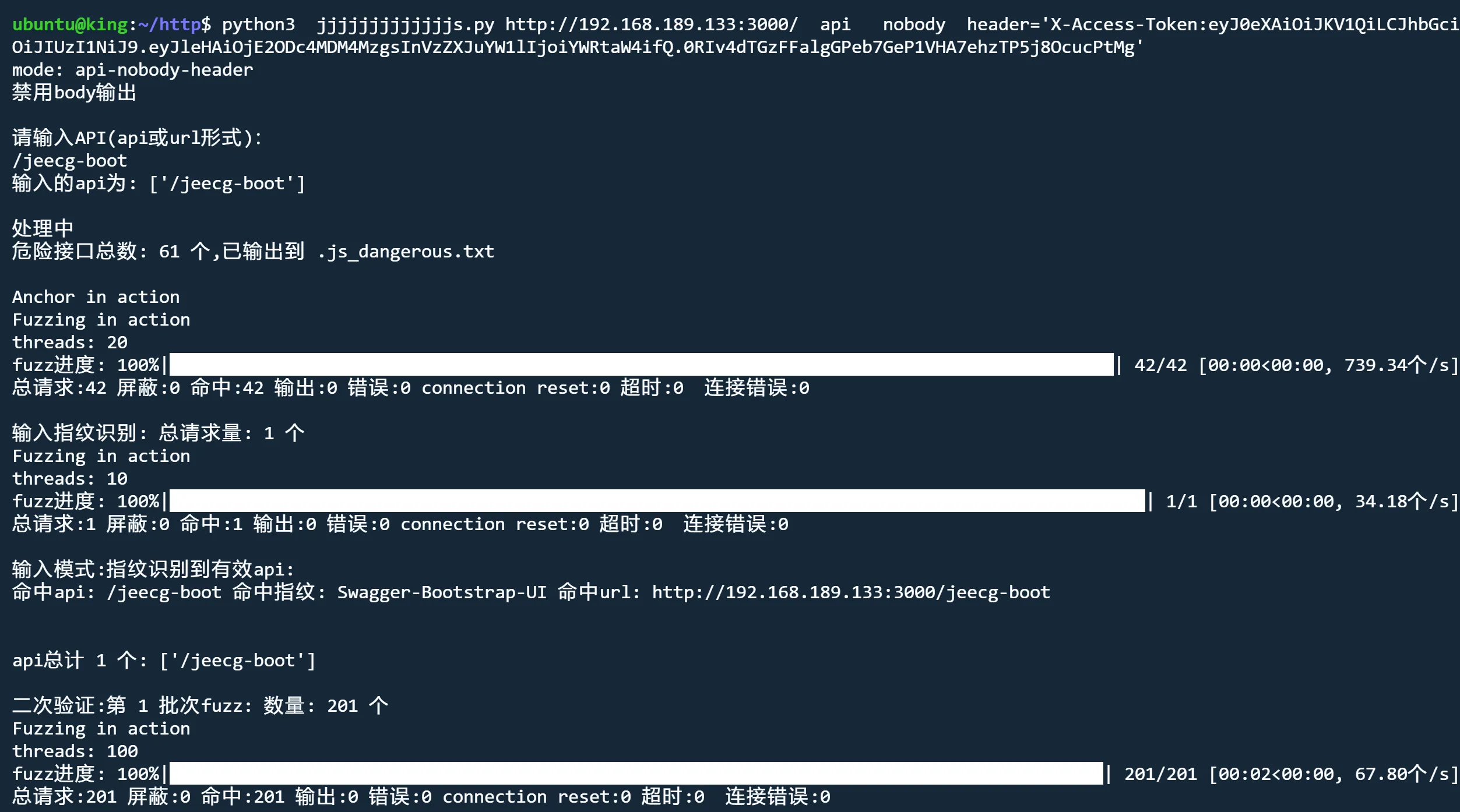
bypass模式 自动实施常见bypass
fuzz模式 nobody bypass
python3 jjjjjjjjjjjjjs.py http://192.168.189.133:3000/ fuzz nobody bypass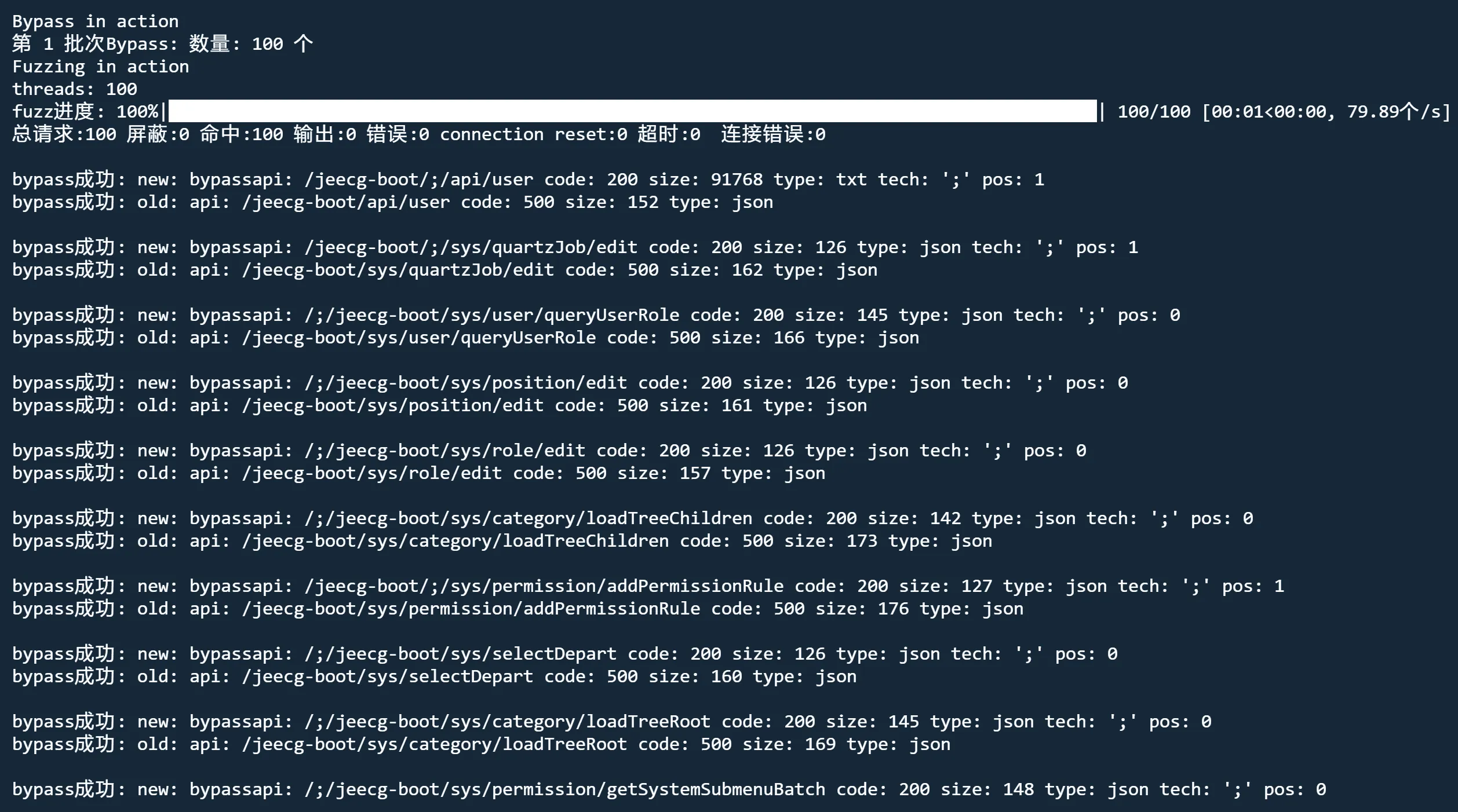
danger模式 解除危险接口限制
python3 jjjjjjjjjjjjjs.py http://192.168.189.133:3000/ fuzz nobody danger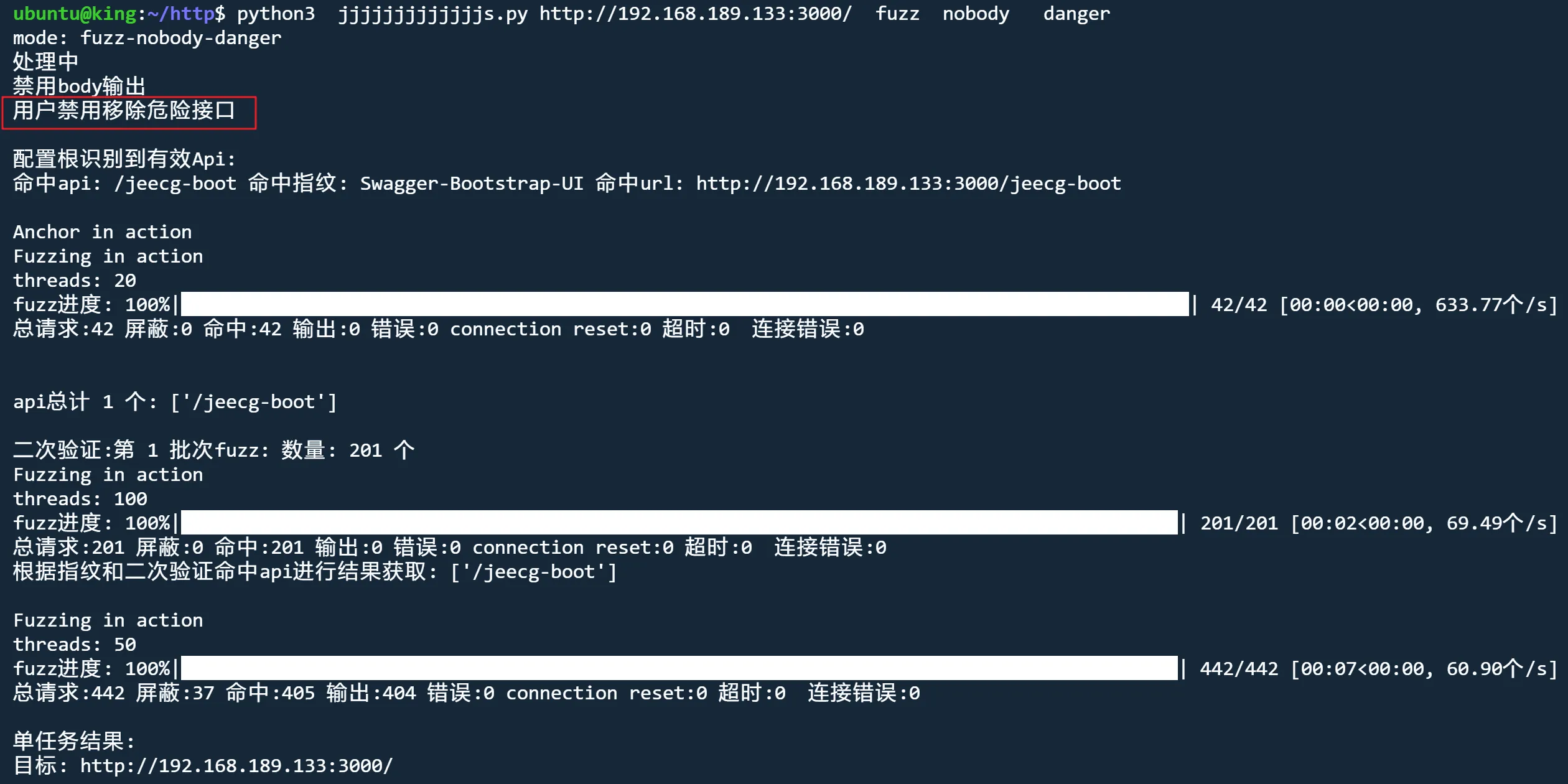
下载地址
项目地址
GitHub:
https://github.com/ttstormxx/jjjjjjjjjjjjjs
转载请注明出处及链接